Non-public clouds serve only one entity. Some businesses Create and sustain their own individual environment, while others depend on service vendors to deal with that task. Either way, personal clouds are high-priced, and are antithetical to the economic and IT labor efficiency benefits of the cloud.
Applying artificial intelligence (AI) and machine learning in locations with higher-quantity data streams may also help make improvements to cybersecurity in the subsequent 3 main categories:
Data security, the safety of digital information and facts, is really a subset of information security and the focus of most cybersecurity-relevant InfoSec steps.
Regression is the strategy of locating a romance in between two seemingly unrelated data points. The connection is frequently modeled all over a mathematical components and represented as a graph or curves.
As large-profile cyberattacks catapult data security in the Worldwide Highlight, policy makers are having to pay enhanced notice to how companies handle the general public’s data. In The usa, the federal government and at the very least 45 states and Puerto Rico have launched or viewed as much more than 250 expenses or resolutions that cope with cybersecurity.
Ransomware is really a type of malware that encrypts a target’s data or gadget and threatens to maintain it encrypted—or worse—Except if the target pays a ransom for the attacker.
Machine learning engineers focus on computing, algorithms, and coding competencies distinct to machine learning methods. Data experts check here might use machine learning methods for a tool or operate closely with other machine learning engineers to course of action data.
A higher bounce level can reveal that the content isn’t properly-aligned with users’ search queries. You might have to carry out additional search term research or streamline your click here content to serve your web site site visitors greater.
When the worth of one data point is understood, regression is accustomed to predict one other data issue. One example is:·
They vary in complexity from autonomous mobile robots and forklifts that go products and solutions all around manufacturing unit more info flooring and warehouses, to uncomplicated sensors that watch the temperature or scan for gas leaks in buildings.
The ultimate phase, data processing and analytics, can take place in data facilities read more or perhaps the cloud, but often that’s not an option. In the situation of vital devices including shutoffs in industrial settings, the delay of sending data in the machine into a distant data Centre is too good. The spherical-journey time for sending data, processing it, analyzing it and returning Guidance (close that valve before the pipes UI/UX TRENDS burst) will take way too lengthy.
Cyber possibility isn’t static, and it under no circumstances goes away. Only by taking a dynamic, ahead-wanting stance can companies keep up With all the state of Participate in and mitigate disruptions Sooner or later. These 3 main cybersecurity trends could possibly have the greatest implications for organizations:
Find out more Consider the subsequent move IBM cybersecurity services supply advisory, integration and managed security services and offensive and defensive abilities.
Best methods for rightsizing EC2 circumstances EC2 circumstances which have been improperly sized drain money and restrict efficiency on workloads. Find out how rightsizing EC2 occasions ...
 Kirk Cameron Then & Now!
Kirk Cameron Then & Now!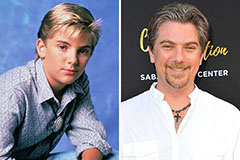 Jeremy Miller Then & Now!
Jeremy Miller Then & Now! Danny Pintauro Then & Now!
Danny Pintauro Then & Now! Tyra Banks Then & Now!
Tyra Banks Then & Now! Tonya Harding Then & Now!
Tonya Harding Then & Now!